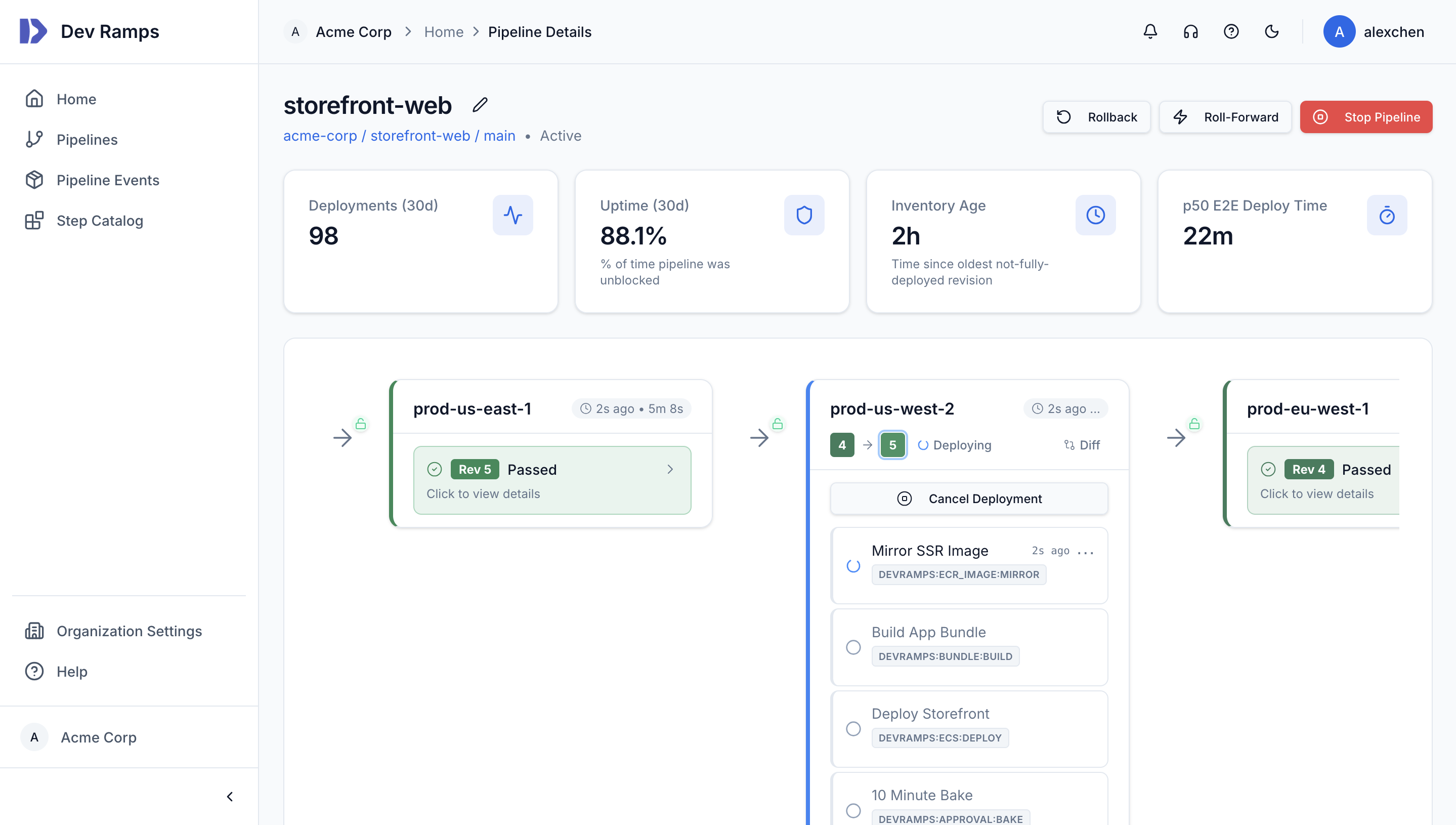
Push code — Dev Ramps handles the rest
Push to your repository and watch your code flow through build, test, and deployment stages across AWS accounts. Artifacts are built, Terraform is applied, services are deployed, and bake periods are observed — all orchestrated automatically.
Approvals, rollbacks, deployment time windows, and CloudWatch alarm-triggered auto-rollback are all handled for you. Access real-time logs, view deployment history, and maintain a complete audit trail of every change.